Fix Azure Blob Storage SAS Token and Authentication Errors with RcloneView
Azure Blob Storage authentication can be tricky, with multiple methods and subtle misconfiguration pitfalls. RcloneView simplifies the setup process and helps you troubleshoot 401/403 errors quickly.
Azure Blob Storage is a powerful and widely used object storage service, but connecting to it from rclone requires getting authentication exactly right. Whether you are using access keys, SAS tokens, or service principals, a single misconfigured parameter can result in cryptic error messages that block your workflow entirely.
This guide covers the most common Azure Blob Storage authentication errors encountered with rclone, explains the different auth methods available, and walks you through fixing each issue using RcloneView's visual remote configuration.
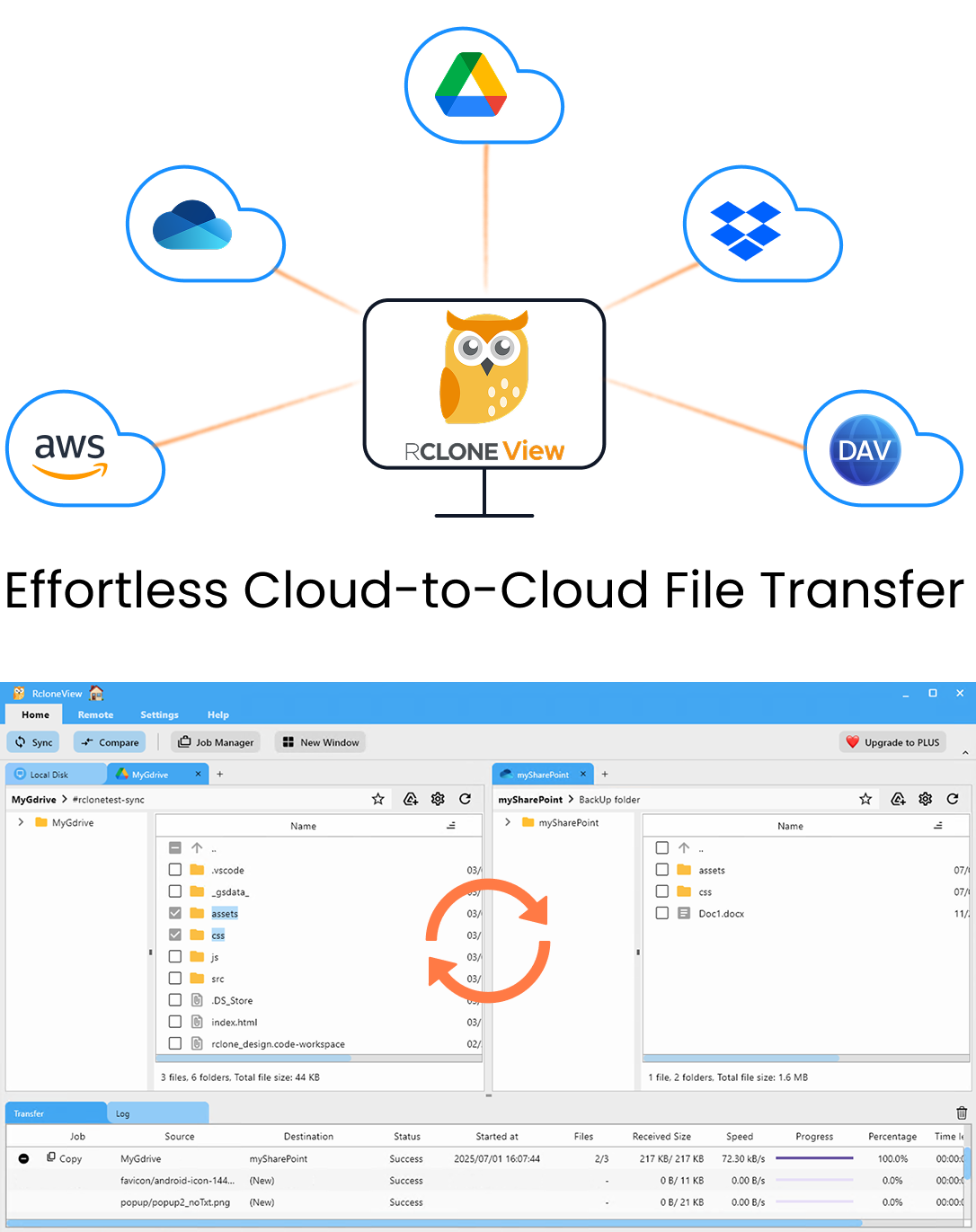
Manage & Sync All Clouds in One Place
RcloneView is a cross-platform GUI for rclone. Compare folders, transfer or sync files, and automate multi-cloud workflows with a clean, visual interface.
- One-click jobs: Copy · Sync · Compare
- Schedulers & history for reliable automation
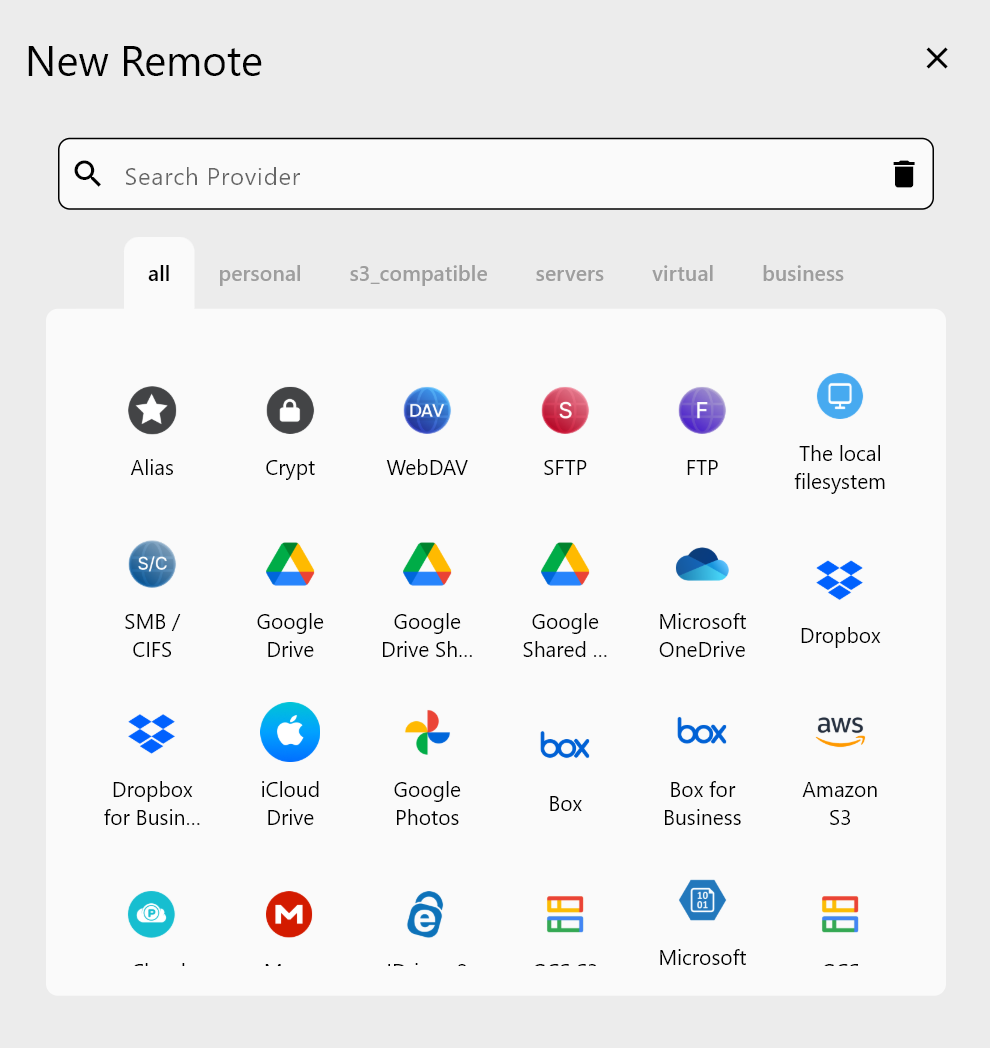
- Works with Google Drive, OneDrive, Dropbox, S3, WebDAV, SFTP and more
Free core features. Plus automations available.
Azure Authentication Methods Overview
Azure Blob Storage supports several authentication methods through rclone. Understanding which one you are using is the first step in troubleshooting:
- Storage Account Access Key: A shared key that grants full access to the entire storage account. Simple but powerful -- treat it like a root password.
- SAS Token (Shared Access Signature): A scoped token that grants limited access with specific permissions, time bounds, and optional IP restrictions. More secure than access keys for external sharing.
- Service Principal (Azure AD): OAuth-based authentication using an Azure AD application. Best for enterprise environments with role-based access control.
- Managed Identity: Available when running from within Azure (e.g., an Azure VM). Uses Azure's identity service automatically.
Each method has its own configuration parameters and failure modes. The sections below address the most common errors for each.
Expired SAS Token (401 Unauthorized)
The single most common SAS token error is expiration. SAS tokens have a start time and an expiry time. Once the token expires, every request returns a 401 Unauthorized or 403 AuthenticationFailed error.
Symptoms:
HTTP 401: Server failed to authenticate the request.
AuthenticationFailed: Signed expiry time must be after signed start time.
How to fix:
- Open the Azure Portal and navigate to your Storage Account.
- Go to Shared access signature under the Security + networking section.
- Set a new expiry date with a generous window (e.g., 1 year for personal use, shorter for shared access).
- Generate a new SAS token.
- In RcloneView, edit your Azure Blob remote and replace the old SAS token with the new one.
- Test the connection to confirm access is restored.
Wrong SAS Token Permissions (403 Forbidden)
A SAS token can be valid but lack the permissions needed for your operation. For example, a token with only Read permission will fail when rclone tries to upload, delete, or list containers.
Symptoms:
HTTP 403: This request is not authorized to perform this operation.
AuthorizationPermissionMismatch
Required permissions for rclone operations:
| Operation | Required SAS Permissions |
|---|---|
| List containers | List |
| Browse files | Read, List |
| Upload files | Write, Create |
| Delete files | Delete |
| Full sync | Read, Write, Delete, List, Create |
How to fix: Generate a new SAS token in the Azure Portal with all required permissions. For rclone sync operations, you typically need Read, Write, Delete, List, Add, and Create. When in doubt, enable all permissions for your personal storage account.
IP Restriction Blocking Access (403 Forbidden)
SAS tokens can be restricted to specific IP addresses or ranges. If you generated the token while on your office network but try to use it from home, the IP restriction will block you.
Symptoms:
HTTP 403: This request is not authorized to perform this operation using this source IP.
How to fix:
- Generate a new SAS token without IP restrictions, or
- Add your current IP address to the allowed range in the SAS token configuration, or
- Use a Storage Account access key instead, which is not subject to IP restrictions.
If you are on a dynamic IP (most home connections), avoid using IP-restricted SAS tokens unless you can update them regularly.
Access Key Errors (401 Unauthorized)
If you are using a Storage Account access key, errors usually mean the key is wrong or the account name is incorrect.
Common causes:
- Copying the key with trailing whitespace or newline characters.
- Using Key1 when it has been rotated and Key2 is now active.
- Misspelling the storage account name.
- Using the connection string instead of just the key.
How to fix in RcloneView:
- Go to the Azure Portal, navigate to your Storage Account, and open Access keys.
- Click Show next to Key1 or Key2, then copy the key carefully.
- Edit your Azure Blob remote in RcloneView and paste the key into the
keyfield. - Double-check that the
accountfield matches your storage account name exactly (case-sensitive). - Test the connection.
Service Principal Configuration Errors
Service principal authentication requires three values: tenant ID, client ID, and client secret. Missing or incorrect values for any of these will cause authentication failures.
Symptoms:
HTTP 401: AADSTS7000215: Invalid client secret provided.
HTTP 401: AADSTS70001: Application with identifier 'xxx' was not found.
How to fix:
- In the Azure Portal, go to Azure Active Directory > App registrations.
- Find your application and verify the Application (client) ID.
- Check the Directory (tenant) ID on the overview page.
- Under Certificates & secrets, create a new client secret if the old one expired.
- In RcloneView, update the remote configuration with the correct tenant, client_id, and client_secret values.
- Ensure the service principal has the Storage Blob Data Contributor role assigned on the storage account.
Generating a Correct SAS Token Step by Step
To avoid SAS token issues entirely, follow this process:
- Open the Azure Portal and navigate to your Storage Account.
- Click Shared access signature in the left menu.
- Under Allowed services, select Blob.
- Under Allowed resource types, select Container and Object.
- Under Allowed permissions, select all permissions you need (Read, Write, Delete, List, Add, Create).
- Set Start date to today and Expiry date to a reasonable future date.
- Leave Allowed IP addresses empty unless you need IP restrictions.
- Set Allowed protocols to HTTPS only.
- Click Generate SAS and connection string.
- Copy the SAS token (starts with
?sv=). Remove the leading?when pasting into rclone configuration.
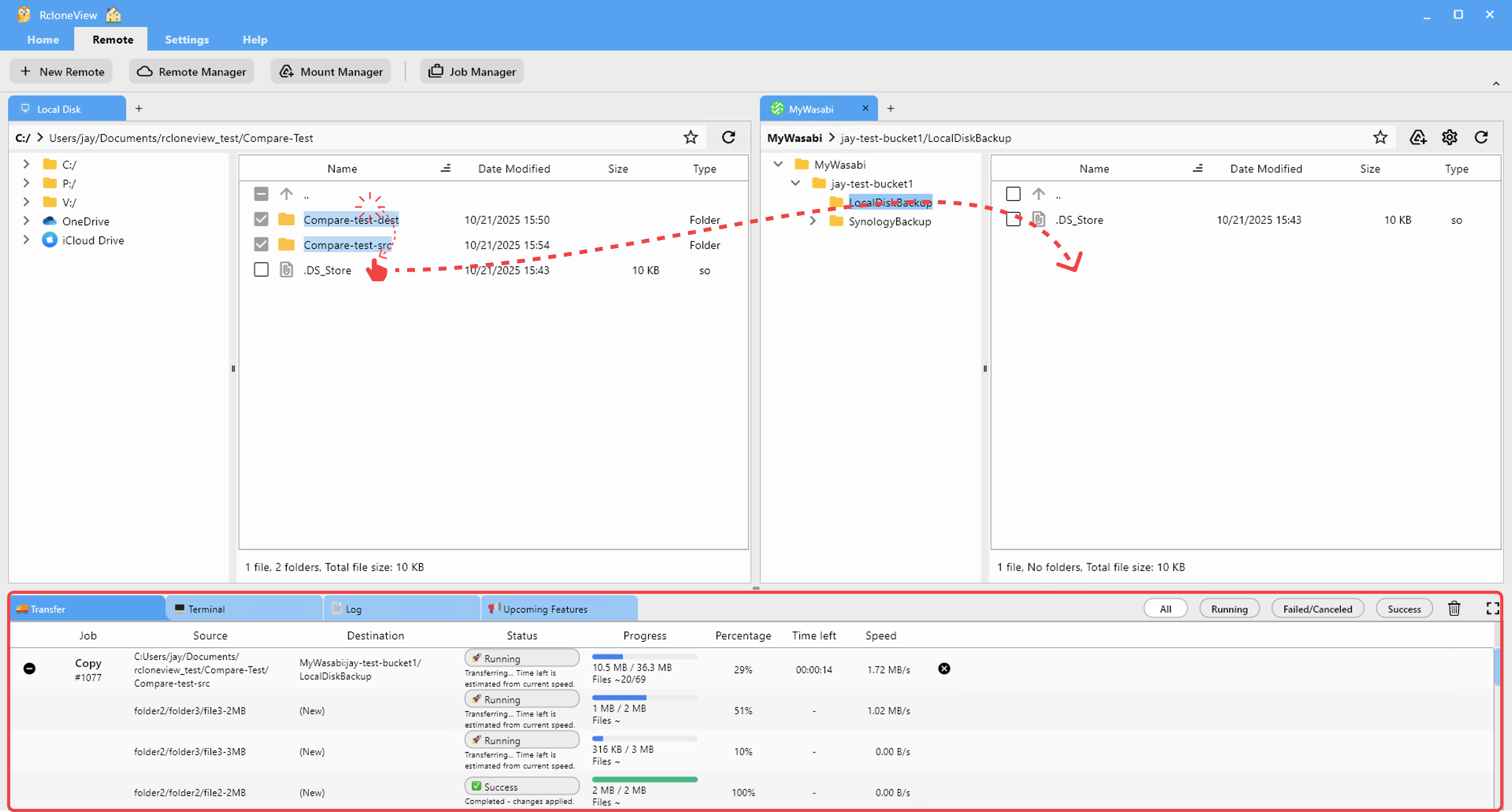
Testing Your Connection in RcloneView
After configuring or updating your Azure Blob remote, test the connection immediately:
- Open the remote in RcloneView's explorer pane.
- Verify that your containers are listed.
- Navigate into a container and confirm you can see files.
- Try uploading a small test file to verify write permissions.
- Delete the test file to confirm delete permissions.
If any step fails, the error message will point you to the specific permission or configuration issue. Address it in the remote configuration and test again.
Getting Started
- Download RcloneView from rcloneview.com.
- Add an Azure Blob Storage remote using your preferred authentication method (access key or SAS token).
- Test the connection by browsing your containers in the explorer pane.
- If you encounter 401 or 403 errors, refer to the relevant section above to diagnose and fix the issue.
Azure authentication errors are almost always caused by expired tokens, missing permissions, or miscopied credentials. Systematic troubleshooting using RcloneView's visual tools makes it straightforward to identify and resolve the issue.
Related Guides: