Cloud Storage Security Checklist — 10 Steps to Protect Your Data Across Multiple Clouds
You trust Google with your documents, Amazon with your backups, and Microsoft with your work files. But are you trusting blindly? This checklist ensures your multi-cloud setup is actually secure.
Using multiple cloud providers multiplies both your storage options and your attack surface. Each cloud account is a potential entry point. Each sync connection is a potential data leak path. This checklist covers the essentials for keeping your multi-cloud storage secure.
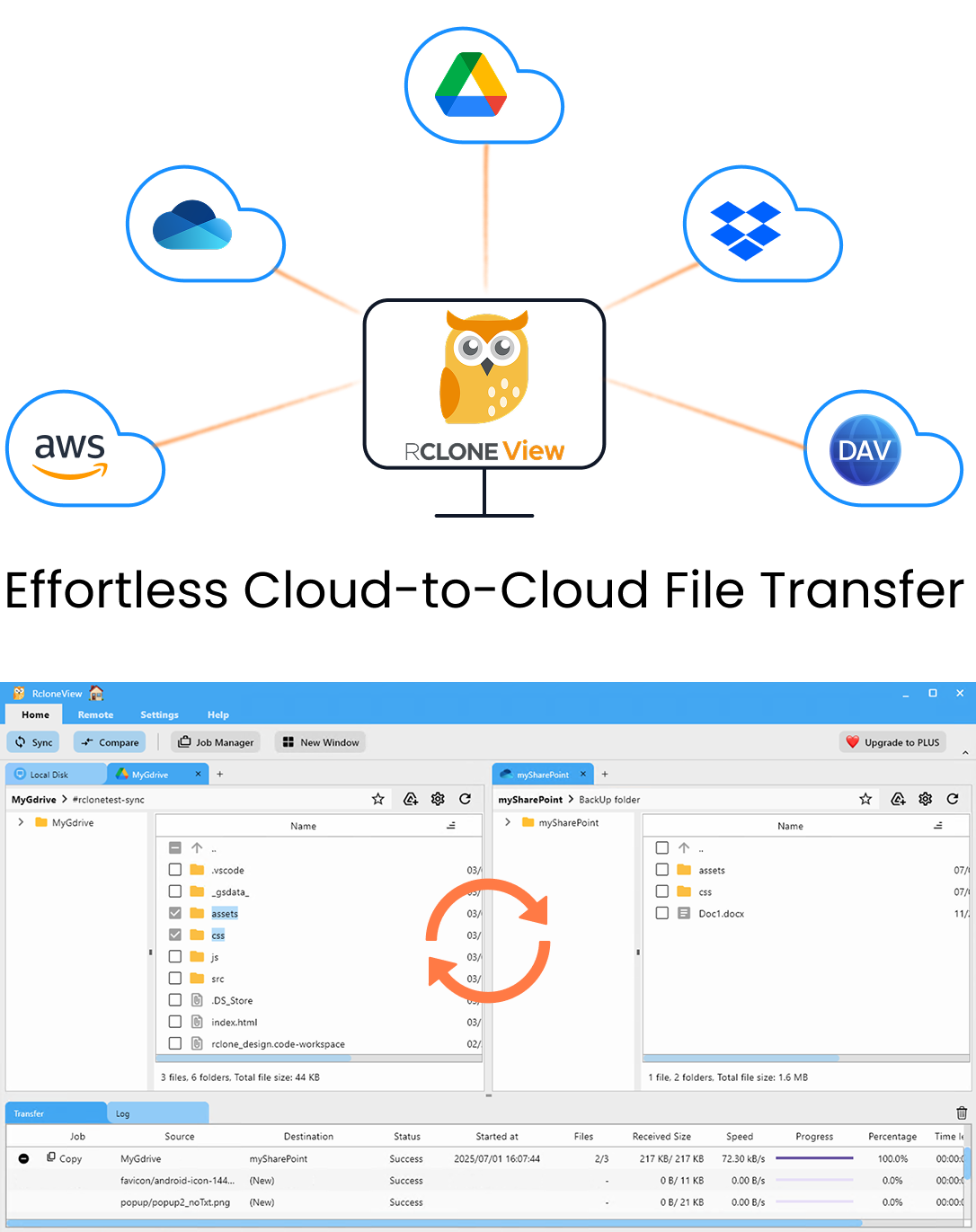
Manage & Sync All Clouds in One Place
RcloneView is a cross-platform GUI for rclone. Compare folders, transfer or sync files, and automate multi-cloud workflows with a clean, visual interface.
- One-click jobs: Copy · Sync · Compare
- Schedulers & history for reliable automation
- Works with Google Drive, OneDrive, Dropbox, S3, WebDAV, SFTP and more
Free core features. Plus automations available.
The Checklist
1) Enable 2FA on every cloud account
Every cloud account should have two-factor authentication enabled. This is the single most effective security measure. Without 2FA, a stolen password means total access to your files.
2) Use unique passwords per service
Never reuse passwords across cloud providers. A breach at one provider shouldn't compromise all your clouds. Use a password manager.
3) Encrypt sensitive data before uploading
Cloud providers encrypt data at rest, but they hold the keys. For truly private data, use client-side encryption (like rclone's crypt remote) so the provider can never read your files.
4) Use local-first tools
Tools that route your data through third-party servers add another party with access to your files. RcloneView's local-first architecture means data flows directly between your machine and your clouds — no intermediary.
5) Review OAuth permissions regularly
Check which apps have access to your Google Drive, OneDrive, and Dropbox. Revoke access for apps you no longer use. Each connected app is a potential attack vector.
6) Use separate credentials for backups
Don't use the same AWS access key for your application and your backup. If the application key is compromised, the backup should remain secure with its own separate credentials.
7) Enable versioning on backup storage
S3 versioning, B2 versioning — enable it. If ransomware or a malicious actor overwrites your files, versioning lets you roll back to clean copies.
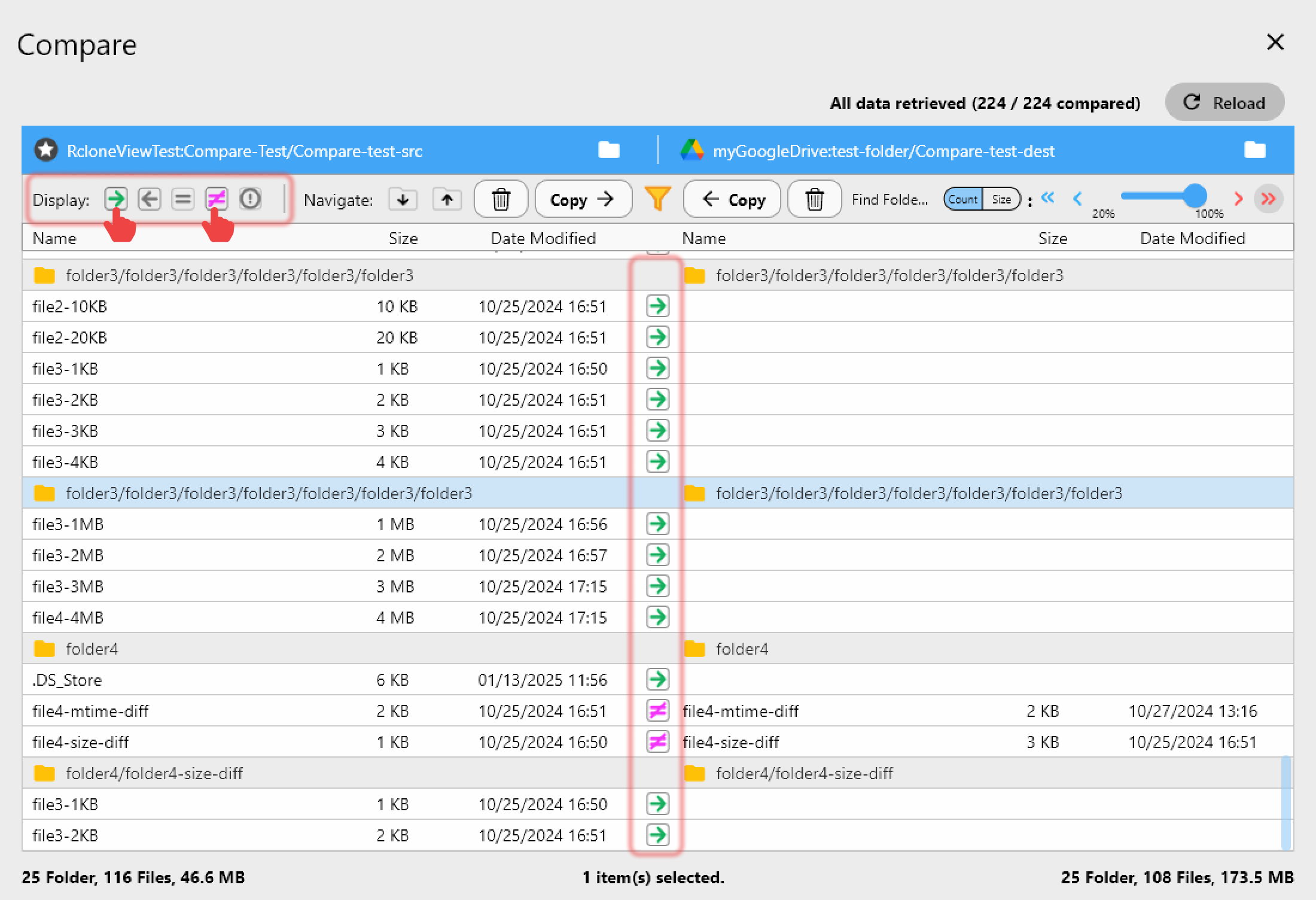
8) Verify backups regularly
A backup you haven't verified is a backup you can't trust. Use Folder Comparison monthly:
9) Monitor for unauthorized access
Review cloud provider access logs. Set up alerts for unusual activity — logins from new locations, bulk downloads, or permission changes.
10) Have a breach response plan
If one cloud account is compromised:
- Change password immediately.
- Revoke all OAuth tokens.
- Check for unauthorized file changes.
- Restore from verified backup.
- Review access logs for scope of breach.
How RcloneView Helps
- Local-first — No third-party server touches your data.
- Crypt remotes — Client-side encryption for sensitive files.
- Folder Comparison — Verify backup integrity.
- Job History — Audit trail of all transfer operations.
- No account required — RcloneView doesn't require you to create an account with them.
Getting Started
- Download RcloneView from rcloneview.com.
- Work through this checklist for each cloud account.
- Set up encrypted backups for sensitive data.
- Schedule monthly verification with Folder Comparison.
Security isn't a feature you enable once. It's a practice you maintain.
Related Guides: