Fix Google Shared Drive Permission Errors — Resolve Access Issues with RcloneView
A 403 Forbidden error on a Shared Drive you should have access to is both confusing and urgent.
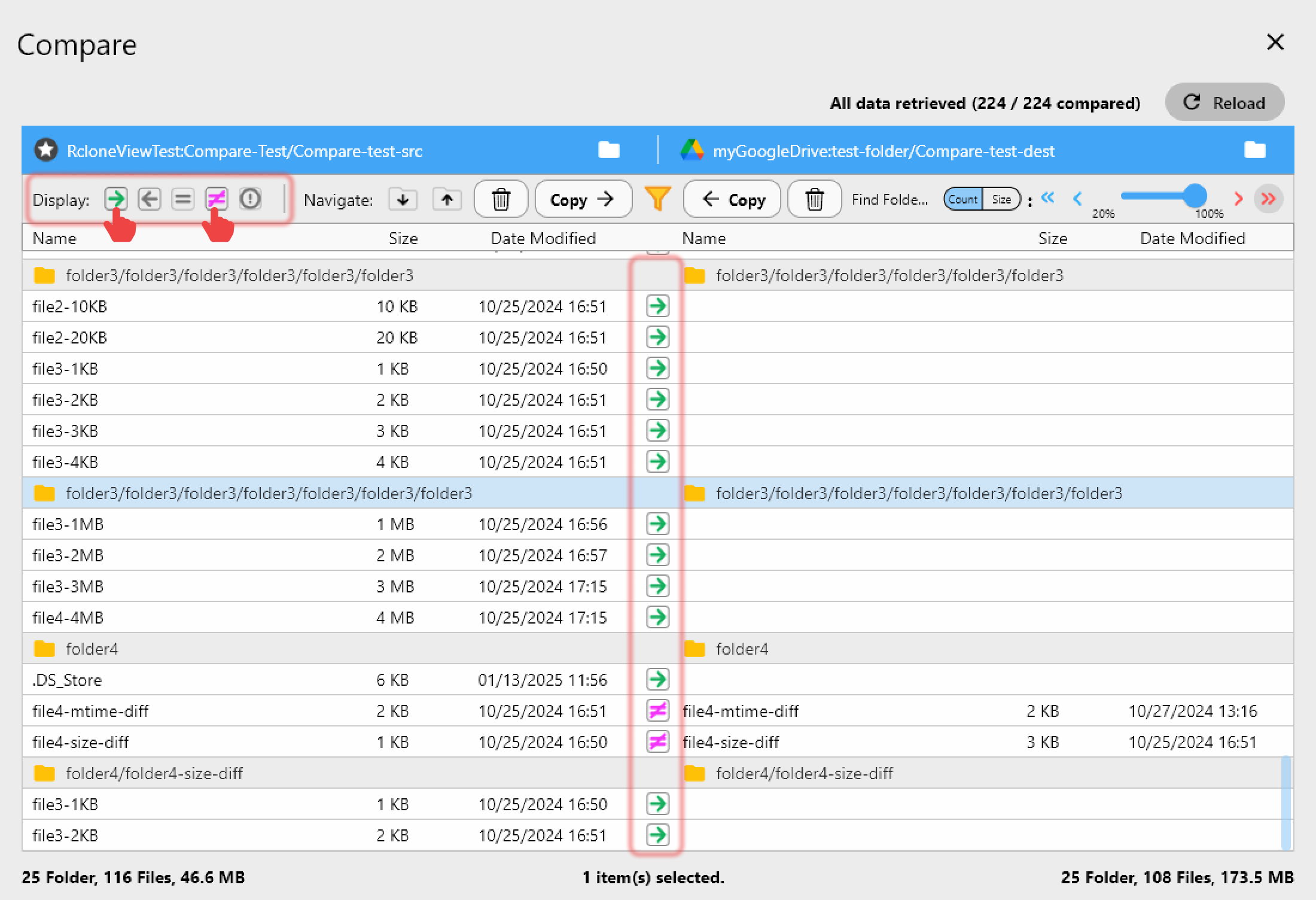
Google Shared Drives (formerly Team Drives) introduce a layered permission model that goes beyond simple file sharing. When sync tools fail to access Shared Drive content, the error messages from Google's API are often vague — "insufficient permissions" could mean a dozen different things. RcloneView streamlines Shared Drive configuration with explicit drive ID selection, proper OAuth scope handling, and clear error reporting that pinpoints the actual permission failure.
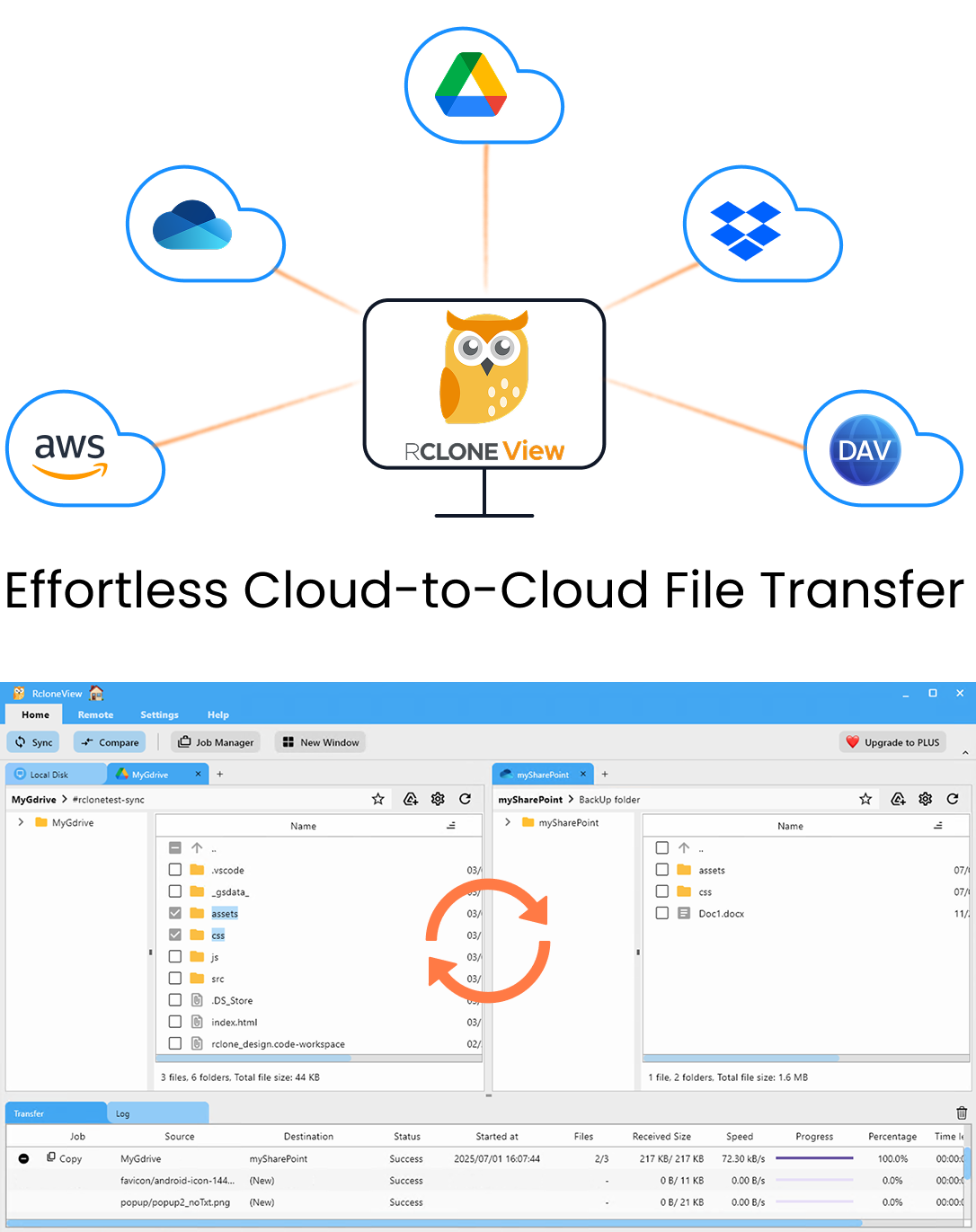
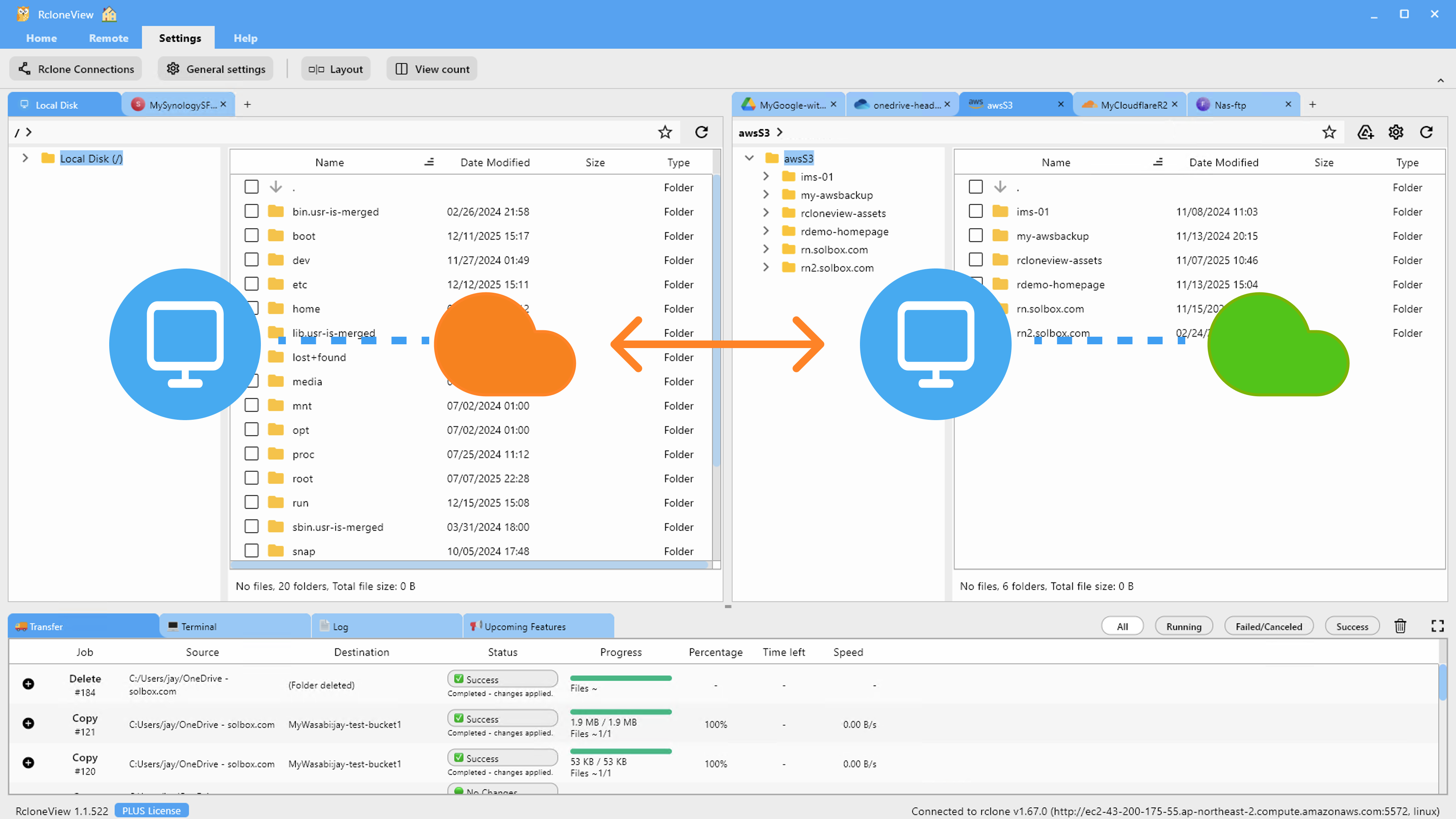
Manage & Sync All Clouds in One Place
RcloneView is a cross-platform GUI for rclone. Compare folders, transfer or sync files, and automate multi-cloud workflows with a clean, visual interface.
- One-click jobs: Copy · Sync · Compare
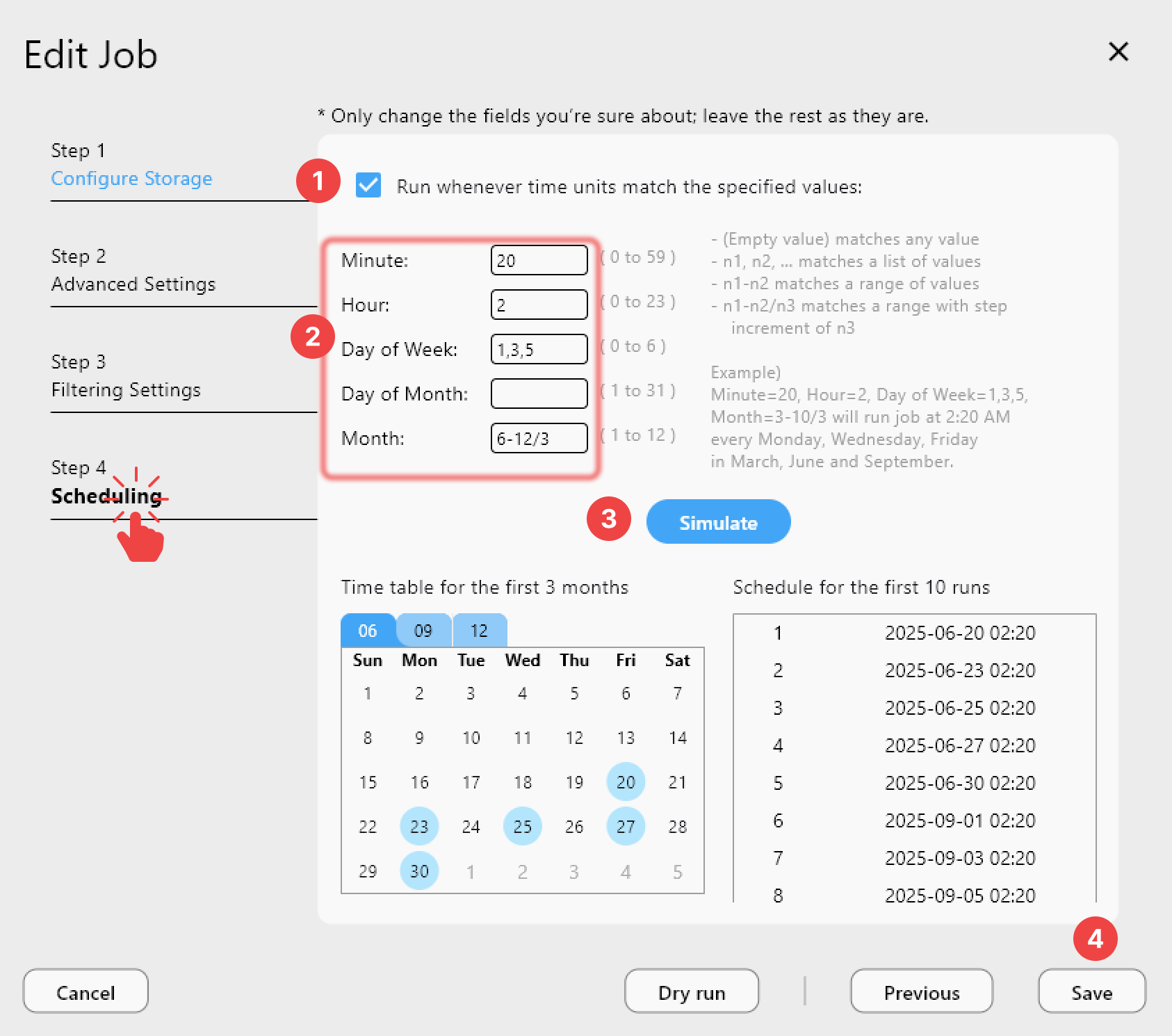
- Schedulers & history for reliable automation
- Works with Google Drive, OneDrive, Dropbox, S3, WebDAV, SFTP and more
Free core features. Plus automations available.
How Shared Drive Permissions Differ
Unlike personal Google Drive, where the account owner has full access to everything, Shared Drives use role-based permissions managed at the organizational level. Members can be assigned Manager, Content Manager, Contributor, Commenter, or Viewer roles, and each role has specific capabilities. A Contributor, for example, can add files but cannot delete or move them — an operation that rclone's sync command may attempt by default.
The critical detail is that Shared Drive access must be explicitly granted at the drive level. Being in the same Google Workspace organization does not automatically grant access. Additionally, domain-wide sharing policies set by the Workspace admin can override individual drive permissions, silently blocking external users or service accounts.
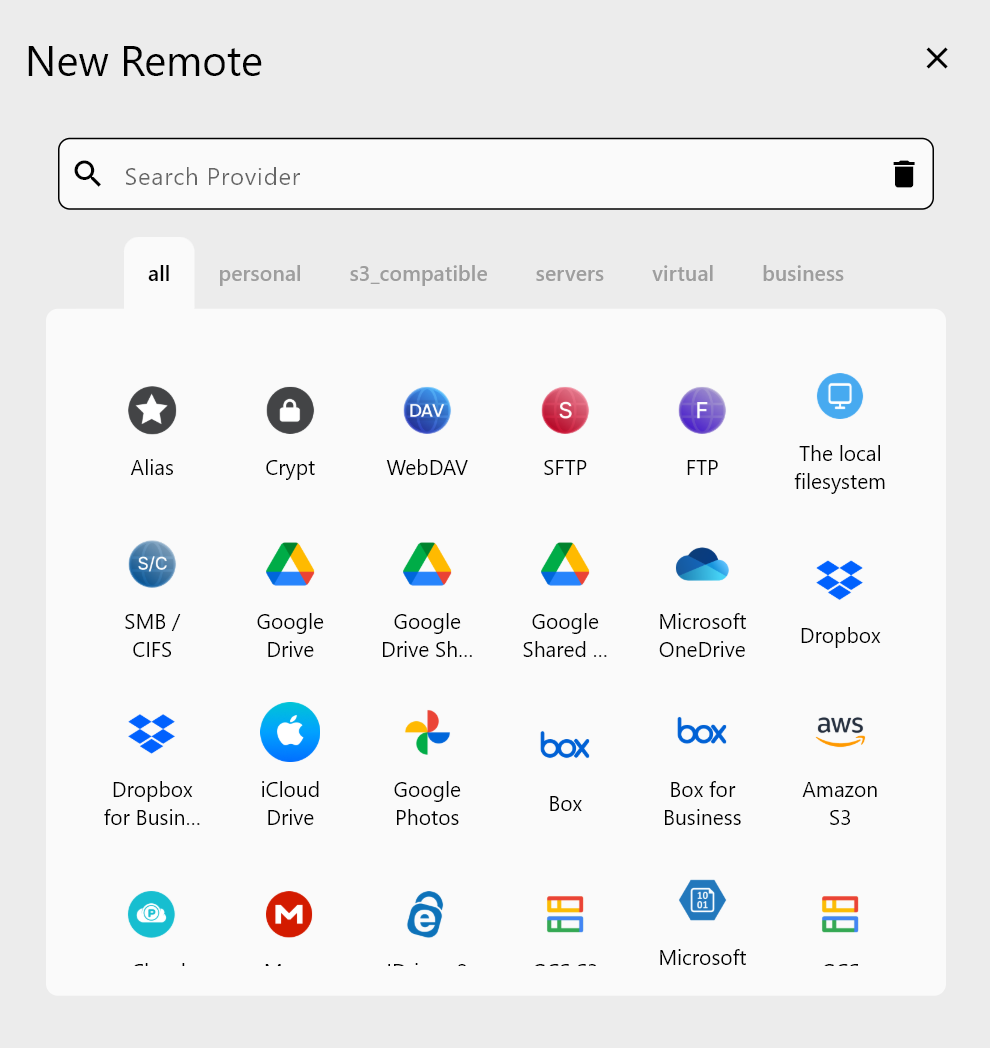
RcloneView's remote configuration wizard prompts you to select a specific Shared Drive by ID, ensuring the connection targets the correct drive rather than defaulting to the user's personal "My Drive."
Configuring OAuth Scopes Correctly
A common source of permission errors is insufficient OAuth scopes. When you first authorize RcloneView with Google, the OAuth consent screen requests specific permissions. If the initial authorization used a read-only scope, all write operations on Shared Drives will fail with a 403 error.
RcloneView requests the drive scope by default, which provides full read-write access. If you previously authorized with a narrower scope, you need to re-authorize by running the config flow again. The token file stores the granted scopes, and RcloneView can detect when the current token lacks the permissions needed for your configured operations.
For Google Workspace environments using service accounts, the service account must be granted domain-wide delegation with the appropriate scopes in the admin console. Without this step, the service account can authenticate but cannot access any Shared Drive content.
Resolving Common Error Scenarios
"File not found" on files that exist: This typically means the rclone remote is pointed at My Drive instead of the Shared Drive. In RcloneView, verify that the team_drive parameter in your remote configuration is set to the correct Shared Drive ID.
"Insufficient permissions" on upload: Check your role on the Shared Drive. Contributors and above can upload, but if an admin has restricted uploads to Managers only, you will get this error. RcloneView's verbose logging (-vv) shows the exact API response, including which permission is missing.
"Rate limit exceeded" during bulk operations: Shared Drives share API quota across all members. A large sync job from one user can exhaust the quota, causing 403 rate-limit errors for everyone. RcloneView's --tpslimit flag throttles API calls to stay within shared quotas.
Service Account and Workspace Admin Settings
For automated workflows, service accounts are the recommended authentication method. The service account must be added as a member of each Shared Drive it needs to access, with at least Content Manager privileges for sync operations that involve deleting files.
Workspace admins should also verify that the "Sharing outside the organization" policy permits the service account's access pattern. If the admin has disabled external sharing, a service account from a different GCP project will be blocked regardless of its Shared Drive membership.
Getting Started
- Download RcloneView from rcloneview.com.
- Configure a Google Drive remote and select your Shared Drive by ID during setup.
- Verify OAuth scopes by re-authorizing if your current token lacks write permissions.
- Check your Shared Drive role — Content Manager or higher is required for full sync operations.
With the right configuration, Shared Drive permission errors disappear and team sync workflows run smoothly.
Related Guides:
- Mount Google Shared Drives with RcloneView
- Fix Permission Denied Cloud Sync Errors — Resolve Access Issues with RcloneView
- Fix Cloud API Rate Limiting Errors — Manage Quotas with RcloneView