Encrypt Cloud Backups with Rclone Crypt — Zero-Knowledge Encryption for Google Drive, S3, and More
When you upload files to Google Drive, Google can read them. When you store data on S3, Amazon can access it. Rclone's crypt remote changes this — your files are encrypted before they ever leave your machine.
Cloud providers encrypt data "at rest" on their servers, but they hold the keys. This means the provider (and potentially government agencies, hackers who breach the provider, or rogue employees) can access your files. Rclone's crypt remote provides true zero-knowledge encryption: files are encrypted on your machine before uploading, and only you have the key.
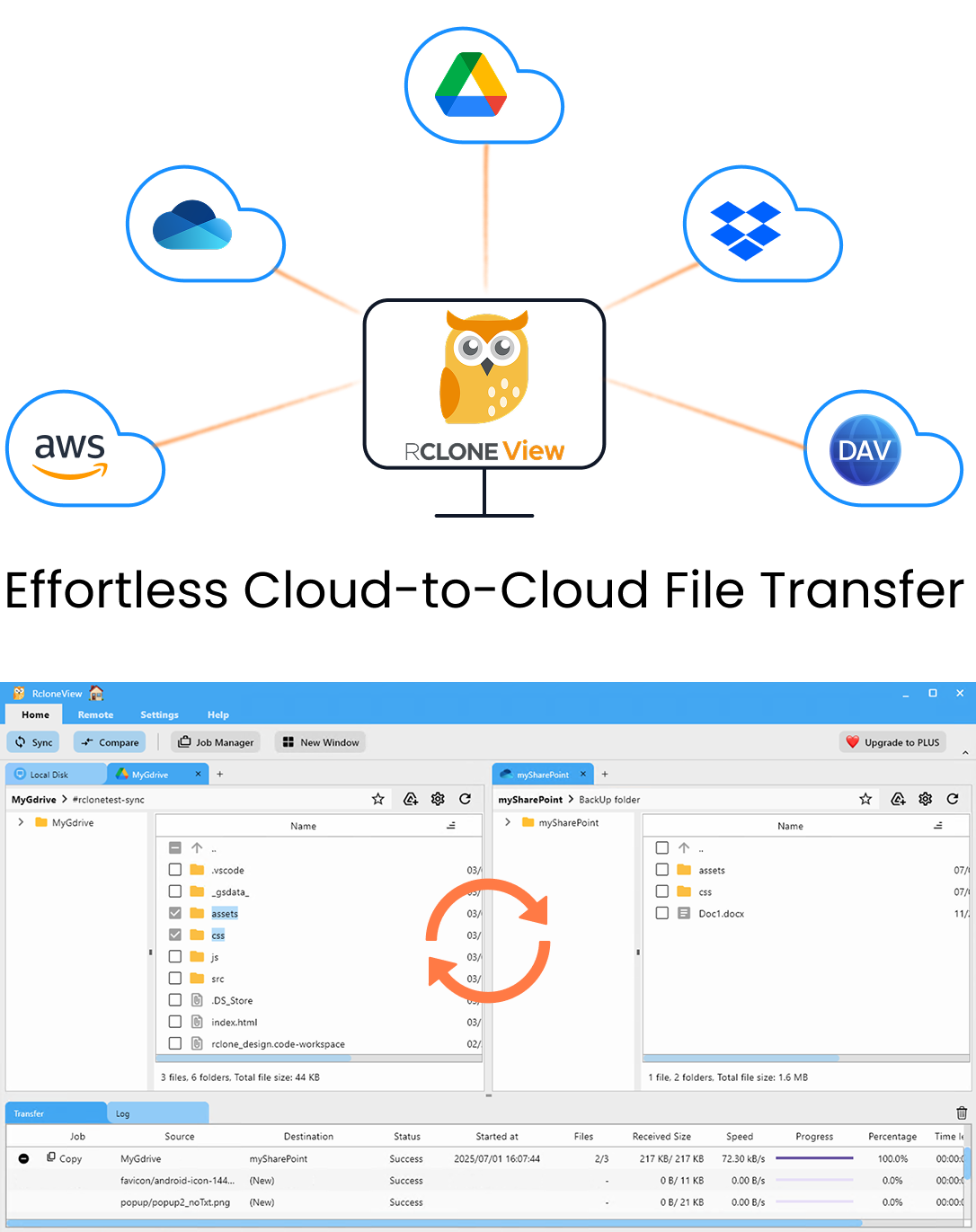
Manage & Sync All Clouds in One Place
RcloneView is a cross-platform GUI for rclone. Compare folders, transfer or sync files, and automate multi-cloud workflows with a clean, visual interface.
- One-click jobs: Copy · Sync · Compare
- Schedulers & history for reliable automation
- Works with Google Drive, OneDrive, Dropbox, S3, WebDAV, SFTP and more
Free core features. Plus automations available.
What Is a Crypt Remote?
A crypt remote is a virtual layer that sits on top of any existing cloud remote:
Your Files → Crypt Remote (encrypts) → Cloud Remote (uploads encrypted blobs)
When you read files:
Cloud Remote (encrypted blobs) → Crypt Remote (decrypts) → Your Files
The cloud provider stores only encrypted data. File names, directory names, and file contents are all encrypted. The provider cannot see what you're storing.
How Crypt Encryption Works
Encryption standards
- File content: AES-256 in CTR mode with HMAC-SHA256 authentication.
- File names: AES-256 EME (encrypt-mix-encrypt) with optional obfuscation.
- Directory names: Same as file names (encrypted by default).
What gets encrypted
| Component | Standard Mode | With Name Encryption |
|---|---|---|
| File contents | ✅ Encrypted | ✅ Encrypted |
| File names | ❌ Visible | ✅ Encrypted |
| Directory names | ❌ Visible | ✅ Encrypted |
| File sizes | ❌ Visible (slightly padded) | ❌ Visible (slightly padded) |
| Directory structure | ❌ Visible | ✅ Encrypted |
Recommendation: Always enable file name encryption for maximum privacy.
Setting Up Crypt in RcloneView
Step 1: Have an existing remote
First, add your cloud storage as a normal remote (e.g., Google Drive, S3, Backblaze B2):
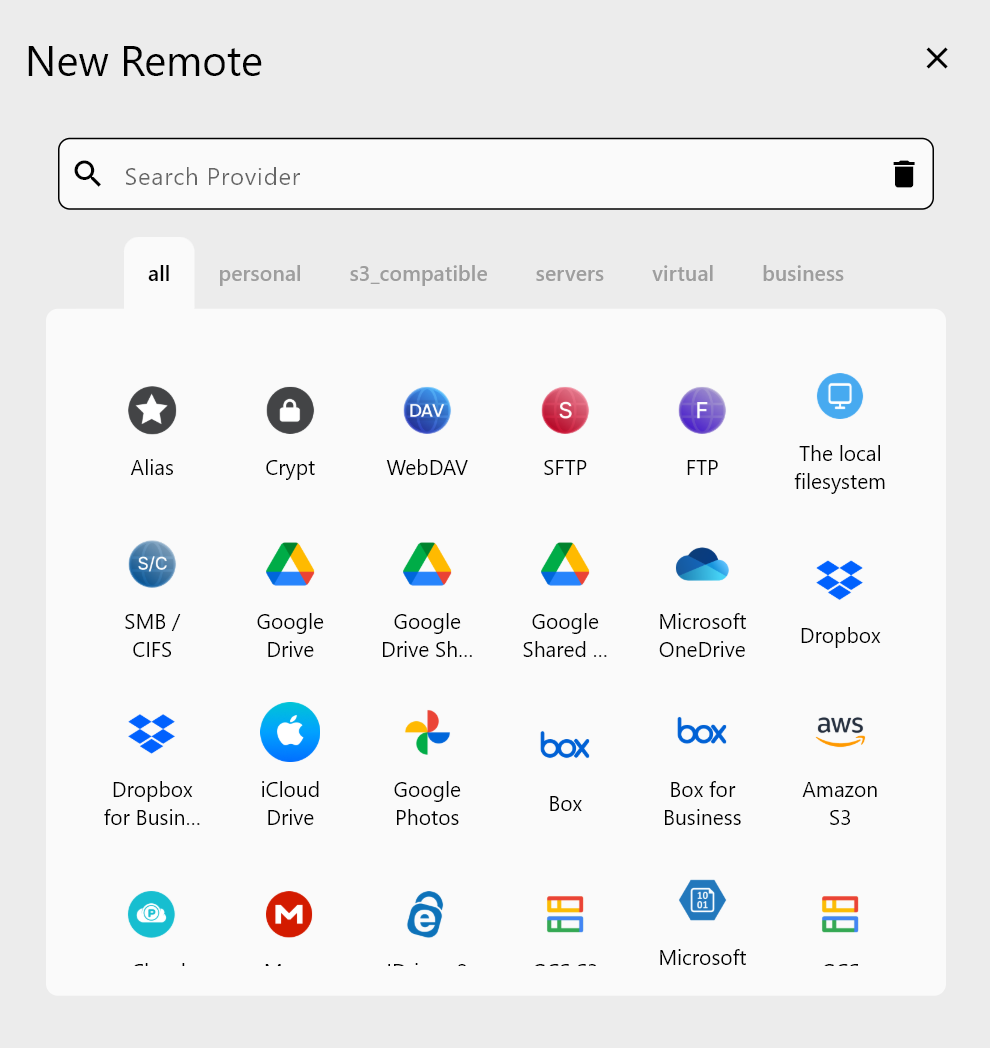
Step 2: Create a crypt remote on top
Add a new remote of type Crypt. Configure it to point at a folder on your existing remote:
- Remote:
gdrive:encrypted-backup/(a folder on your Google Drive). - File name encryption: Standard (encrypted).
- Directory name encryption: True.
- Password: A strong password (this is your encryption key — don't lose it).
- Password2 (salt): An additional password for extra security.
Step 3: Use the crypt remote
Now when you browse or transfer files through the crypt remote, everything is encrypted transparently. Upload through the crypt remote → files arrive encrypted on Google Drive. Download through the crypt remote → files are decrypted automatically.
Encrypted Backup Workflow
Set up an encrypted backup job
Create a Copy job from your local storage (or another cloud) to the crypt remote:
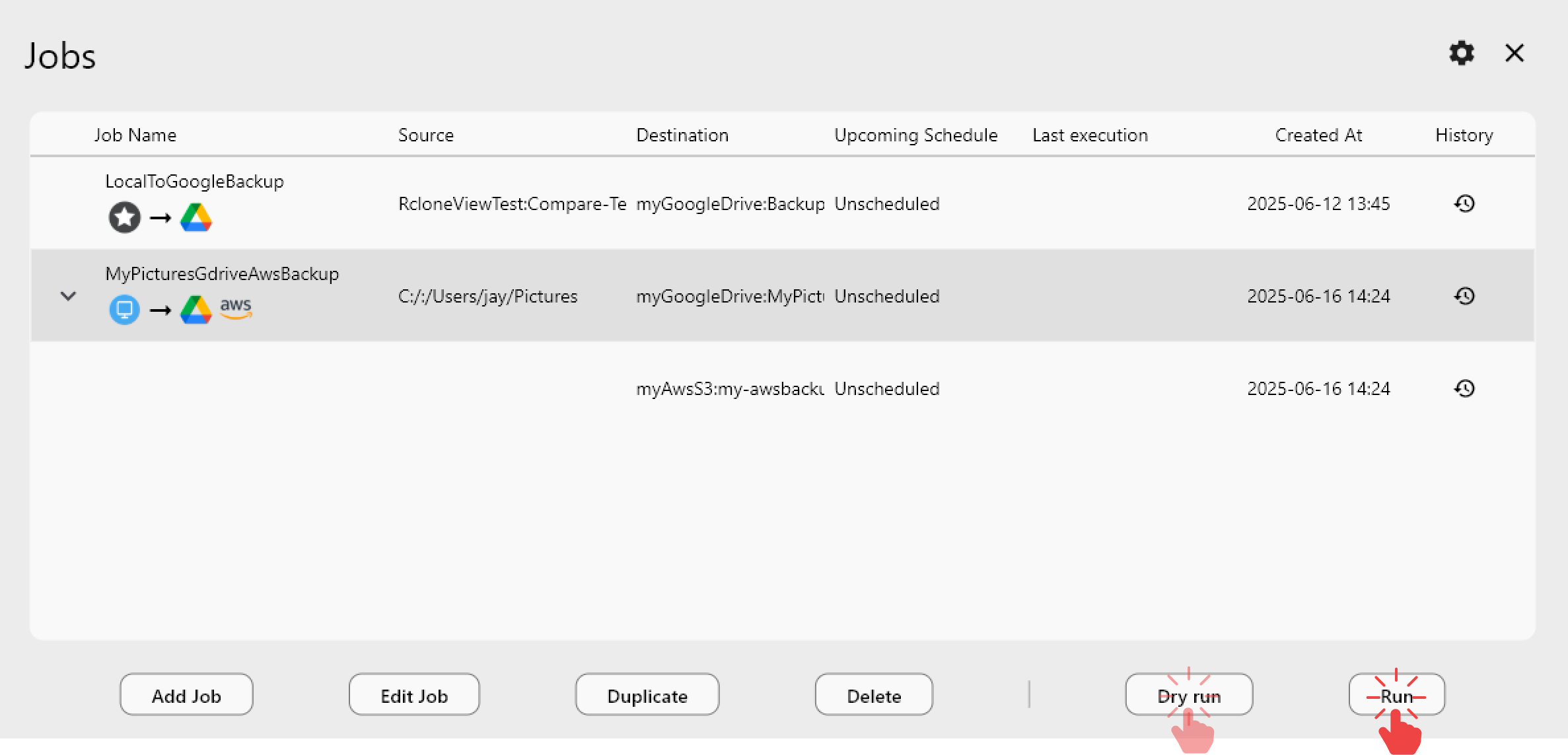
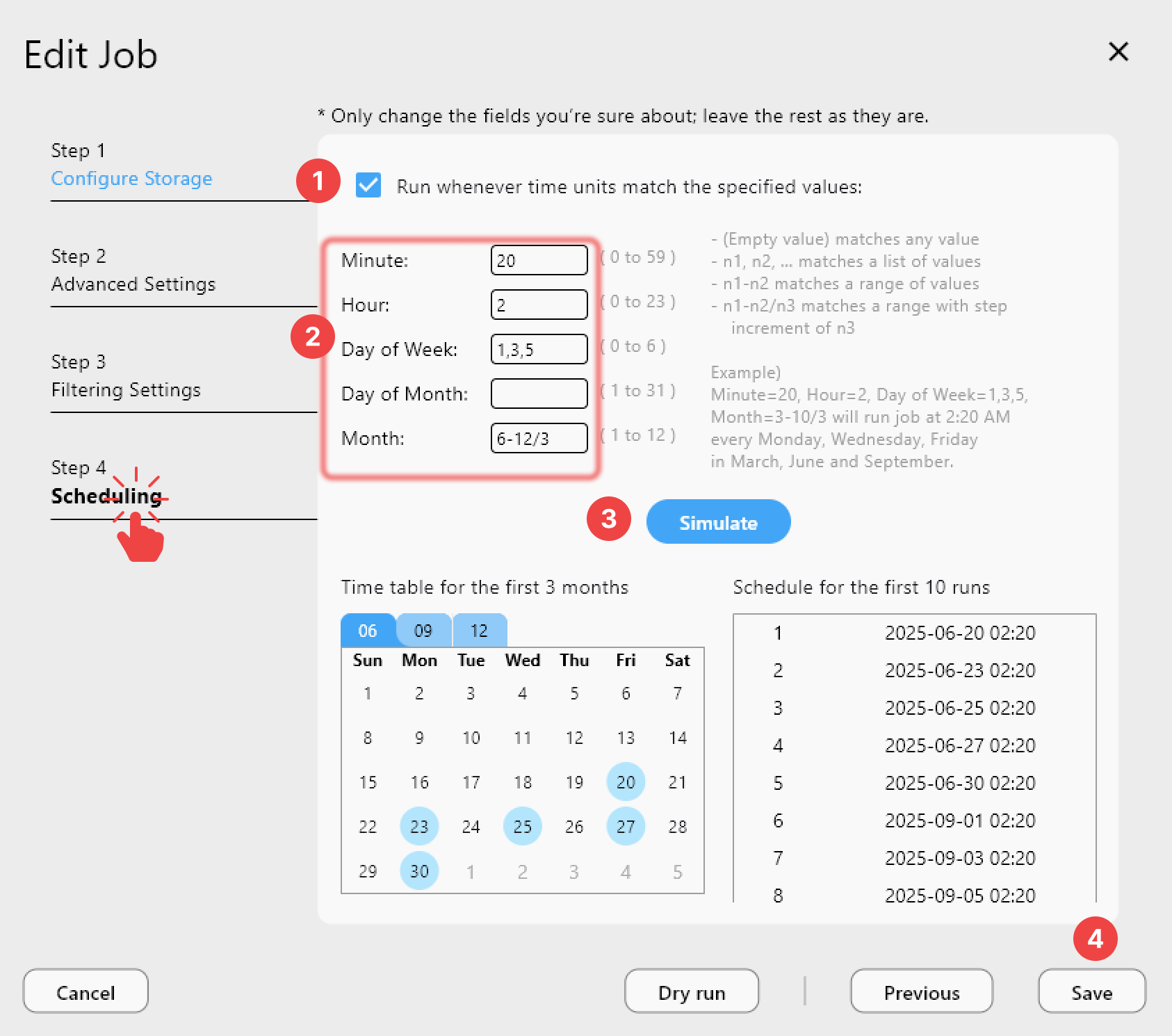
Schedule daily encrypted backups
What the cloud provider sees
If someone browses your Google Drive, they see:
encrypted-backup/
q6r2v8s3f1g4h5j6k7l8/
a1b2c3d4e5f6g7h8i9j0k1l2m3n4.bin
p5q6r7s8t9u0v1w2x3y4z5a6b7c8.bin
m9n0o1p2q3r4s5t6u7v8/
d9e0f1g2h3i4j5k6l7m8n9o0p1q2.bin
File names are unreadable. Contents are encrypted. Even the folder structure is hidden.
What you see (through the crypt remote)
encrypted-backup/
Documents/
tax-return-2025.pdf
passport-scan.jpg
Medical/
lab-results-march.pdf
Normal, readable files — decrypted on the fly.
Practical Use Cases
1) Encrypted Google Drive backup
Your personal Google Drive for daily use. An encrypted backup of sensitive files on the same Google Drive:
gdrive:Documents/ ← Normal files (Google can see)
gdrive-crypt:Sensitive/ ← Encrypted (Google sees only blobs)
2) Encrypted S3 archive
Archive sensitive data on S3 with client-side encryption. Even if your AWS account is compromised, the data is unreadable without your password.
3) HIPAA/compliance storage
Healthcare, legal, and financial data that requires encryption at rest. Crypt remotes provide verifiable client-side encryption.
4) Cross-border data protection
Storing data in cloud regions where you don't fully trust the provider's data access policies.
Verify Encrypted Backups
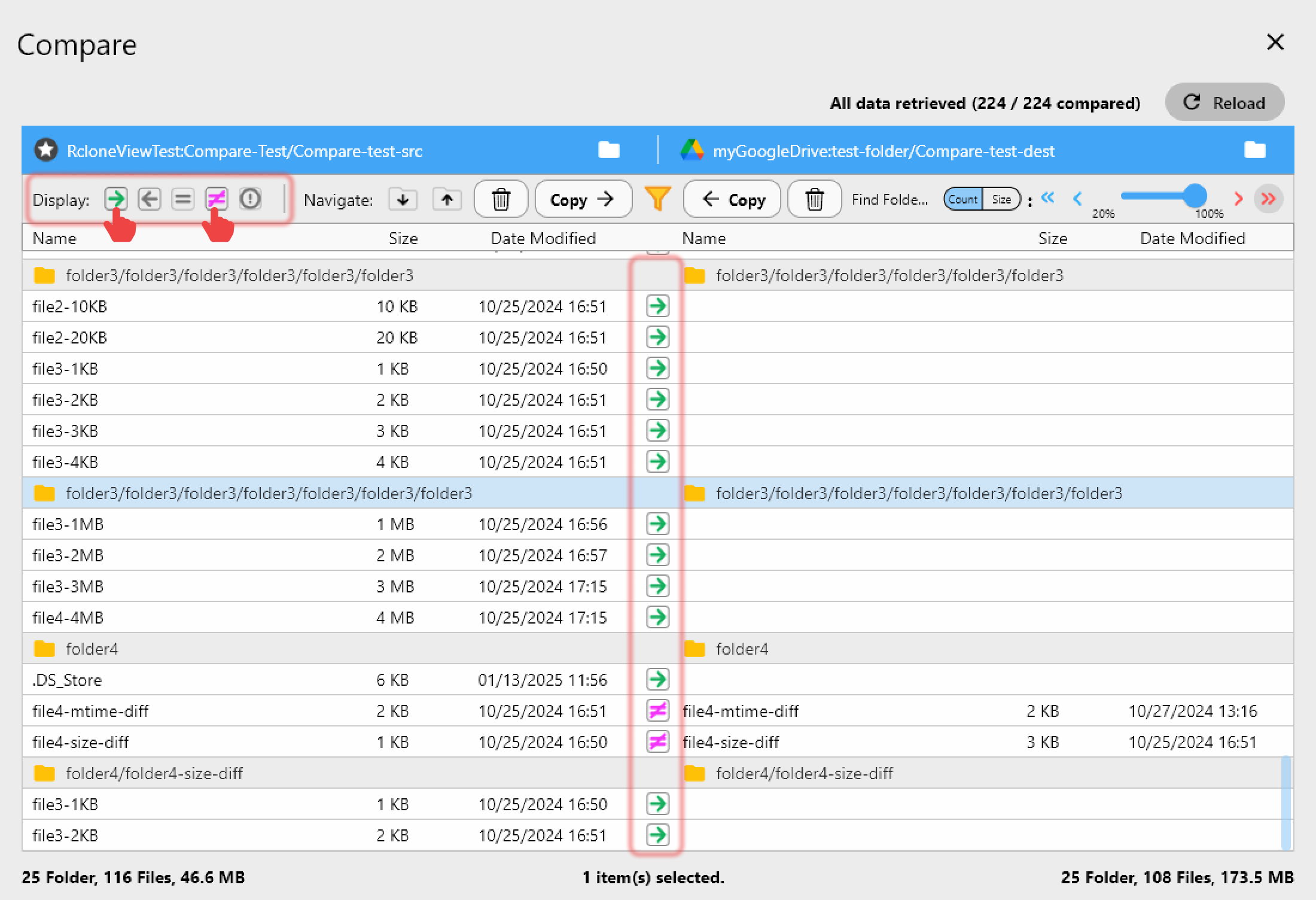
Use Folder Comparison through the crypt remote to verify your encrypted backup matches the source:
Critical Warnings
Don't lose your password
There is no "forgot password" recovery. If you lose your crypt password, your encrypted data is permanently inaccessible. No one — not rclone, not Google, not Amazon — can recover it.
Store your password safely:
- Write it down and store in a physical safe.
- Use a password manager (separate from the cloud you're encrypting).
- Keep at least two copies in different locations.
Don't modify encrypted files directly
Never edit the encrypted blobs directly on the cloud provider. Always access them through the crypt remote. Direct modification will corrupt the files.
Performance impact
Encryption adds some CPU overhead:
- Negligible on modern desktops and laptops.
- Noticeable on Raspberry Pi or low-power devices.
- Doesn't affect network speed (encryption happens before upload).
Multiple Crypt Remotes
You can create different crypt remotes for different purposes:
| Crypt Remote | Points To | Password | Use Case |
|---|---|---|---|
| crypt-personal | gdrive:encrypted/ | Password A | Personal sensitive files |
| crypt-work | s3:work-encrypted/ | Password B | Work documents |
| crypt-archive | b2:archive-encrypted/ | Password C | Long-term archive |
Each uses a different password and different underlying storage.
Getting Started
- Download RcloneView from rcloneview.com.
- Add your cloud storage as a regular remote.
- Create a crypt remote pointing at a folder on that cloud.
- Set a strong password and store it safely.
- Use the crypt remote for all sensitive file operations.
- Schedule encrypted backups for automation.
Your data. Your keys. Your control.
Related Guides: