Cloud Storage for Government and Public Sector Organizations with RcloneView
Government agencies manage some of the most sensitive data on the planet — and the compliance frameworks they operate under demand tools that are transparent, auditable, and flexible enough to work across multiple authorization boundaries.
Federal, state, and local government agencies are accelerating their move to cloud storage. Mandates like the Federal Cloud Computing Strategy and the Cloud Smart initiative push agencies toward commercial cloud services, but the compliance landscape is uniquely demanding. FedRAMP authorization, FISMA controls, NIST 800-171 requirements for Controlled Unclassified Information (CUI), and data sovereignty rules create a web of constraints that commercial file sync tools often cannot satisfy. RcloneView, built on the open-source rclone engine, gives government IT teams a multi-cloud file manager that works with any S3-compatible or cloud storage provider — including those on the FedRAMP marketplace — while keeping data handling transparent and under agency control.
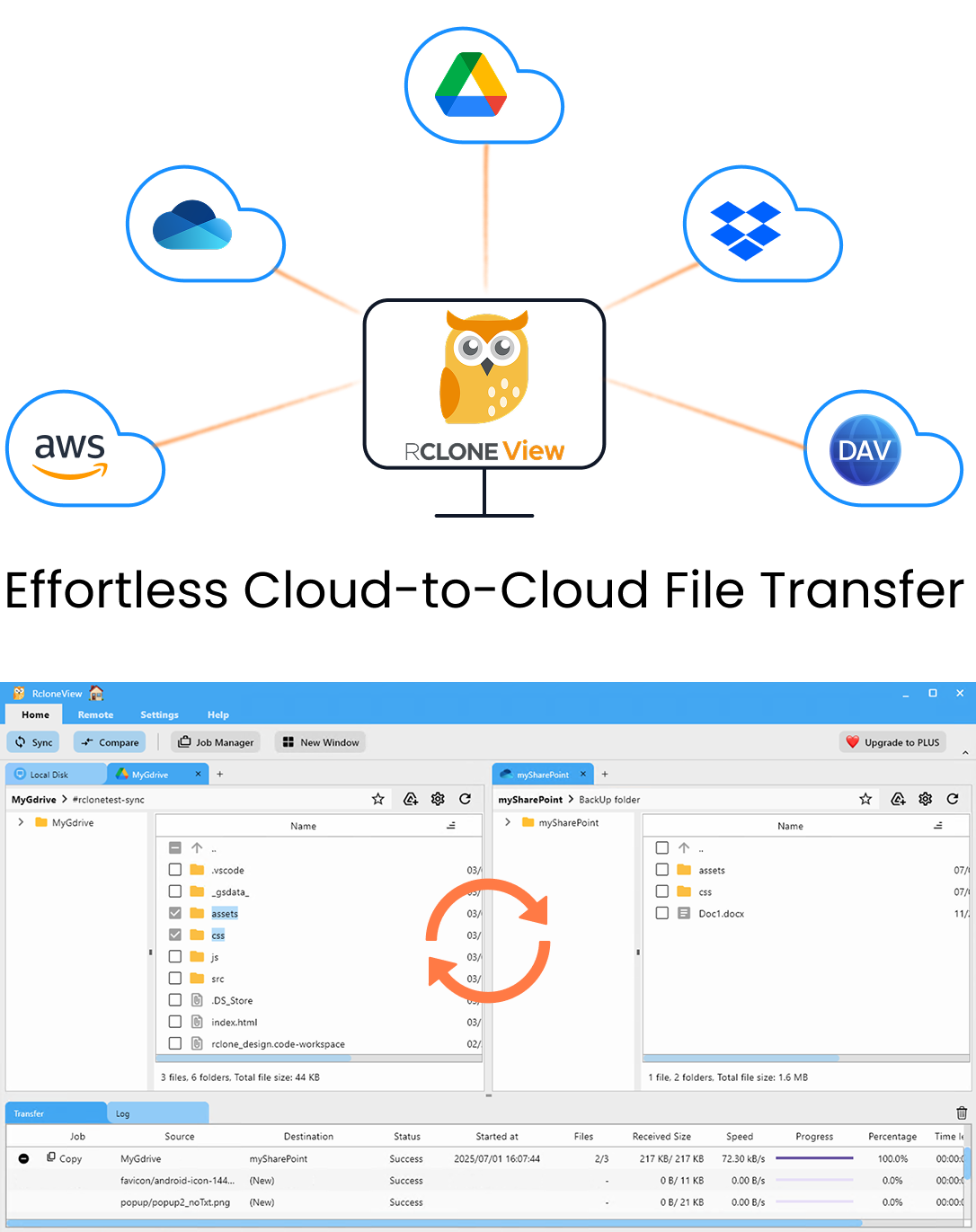
Manage & Sync All Clouds in One Place
RcloneView is a cross-platform GUI for rclone. Compare folders, transfer or sync files, and automate multi-cloud workflows with a clean, visual interface.
- One-click jobs: Copy · Sync · Compare
- Schedulers & history for reliable automation
- Works with Google Drive, OneDrive, Dropbox, S3, WebDAV, SFTP and more
Free core features. Plus automations available.
The Government Cloud Storage Challenge
Government agencies do not have the luxury of picking one cloud vendor and standardizing. Different bureaus may use AWS GovCloud, Azure Government, or Google Cloud Platform with FedRAMP High authorization. Intelligence community workloads may sit on C2S or SC2S environments. State and local agencies often use a mix of commercial and government-specific cloud offerings based on available contracts and cooperative purchasing agreements.
This fragmentation creates real operational problems:
- Data silos across agencies — files needed for interagency collaboration end up in different clouds with different access controls.
- Compliance documentation overhead — every file transfer between systems requires a clear chain of custody and audit trail.
- Vendor lock-in risk — agencies tied to a single provider face cost increases and reduced negotiating leverage at contract renewal.
- Skill gaps — IT staff may be trained on one cloud platform but not another, slowing down cross-cloud operations.
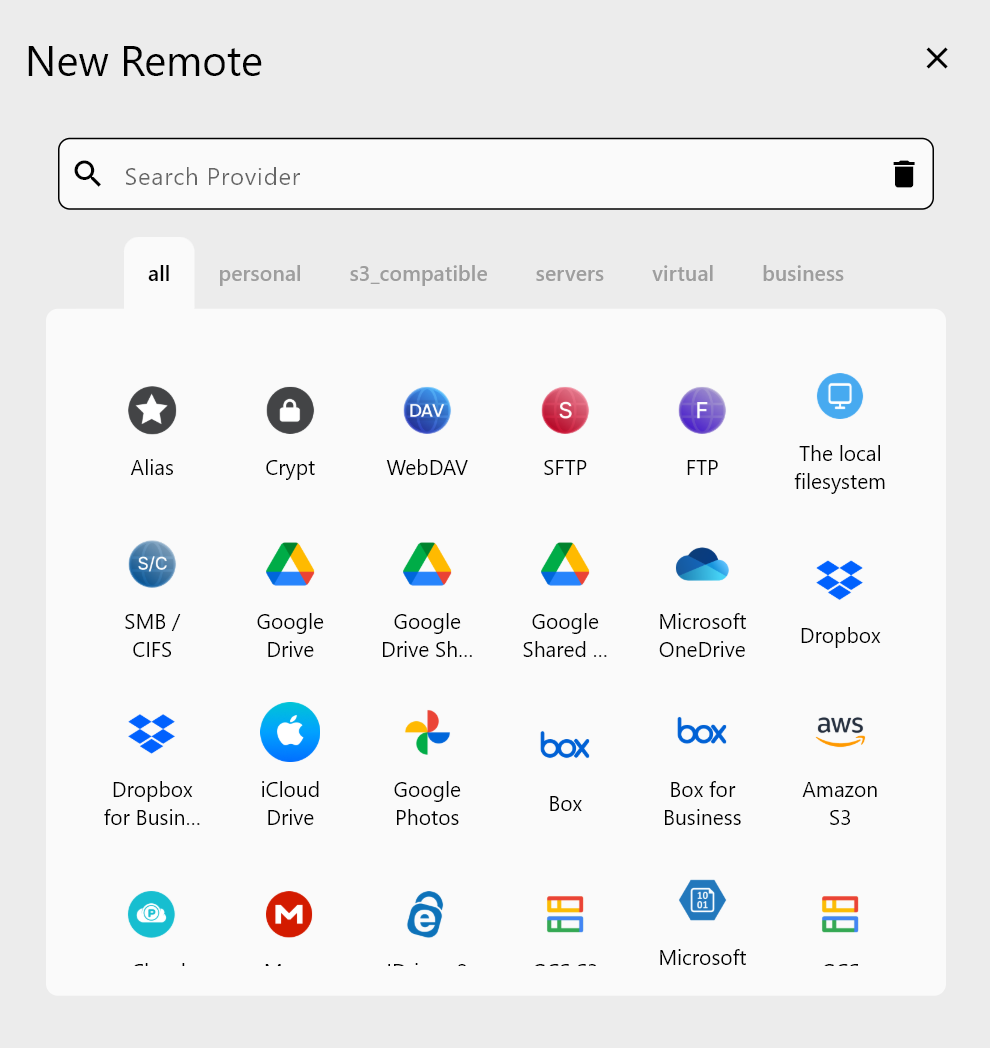
RcloneView addresses these problems by providing a single interface that connects to 70+ cloud storage backends. An agency can manage files on AWS GovCloud, Azure Government, and an on-premise S3-compatible object store from the same window, using the same workflows.
FedRAMP and FISMA Compliance Considerations
FedRAMP (Federal Risk and Authorization Management Program) sets the baseline security requirements for cloud services used by federal agencies. FISMA (Federal Information Security Modernization Act) requires agencies to implement information security programs that align with NIST standards. When using RcloneView for government cloud file management, several compliance considerations apply:
Client-side operation — RcloneView runs entirely on the user's workstation or server. No data passes through third-party relay servers. Files move directly between the agency endpoint and the authorized cloud provider. This simplifies the authorization boundary because the tool itself does not introduce a new cloud service into the system security plan.
Encryption in transit — all connections use TLS by default. For providers that support server-side encryption (SSE-S3, SSE-KMS, SSE-C on AWS, or equivalent on Azure and GCP), RcloneView passes the appropriate headers. Agencies can also layer rclone's built-in client-side encryption (crypt remote) to encrypt files before they leave the workstation, satisfying NIST SP 800-53 SC-8 (Transmission Confidentiality) and SC-28 (Protection of Information at Rest) controls.
Audit logging — RcloneView logs every transfer operation, including source, destination, file size, timestamp, and success or failure status. These logs can be exported and fed into a SIEM or GRC platform to meet AU-2 (Audit Events) and AU-3 (Content of Audit Records) requirements.
Access control alignment — by using the cloud provider's native IAM policies (AWS IAM, Azure RBAC, GCP IAM), agencies maintain their existing access control posture. RcloneView authenticates using service accounts, access keys, or OAuth tokens that inherit the permissions defined in the agency's identity management system.
NIST 800-171 and Controlled Unclassified Information
NIST Special Publication 800-171 governs the protection of Controlled Unclassified Information (CUI) in non-federal systems. Defense contractors, research institutions, and state agencies handling CUI must meet 110 security requirements across 14 control families. Cloud file management touches several of these directly:
- 3.1 Access Control — limit system access to authorized users. RcloneView supports credential-based authentication for each remote, and agencies can restrict which cloud accounts are configured on each workstation.
- 3.5 Identification and Authentication — authenticate users and devices. OAuth 2.0 flows, API keys, and service account credentials used by RcloneView map to the agency's identity provider.
- 3.8 Media Protection — protect CUI on digital media. Client-side encryption via rclone crypt ensures CUI is encrypted before being written to cloud storage, even if the cloud provider's at-rest encryption is also active.
- 3.13 System and Communications Protection — monitor and control communications at external boundaries. RcloneView's direct-to-provider architecture means all traffic flows through the agency's network perimeter controls (firewalls, proxies, DLP sensors).
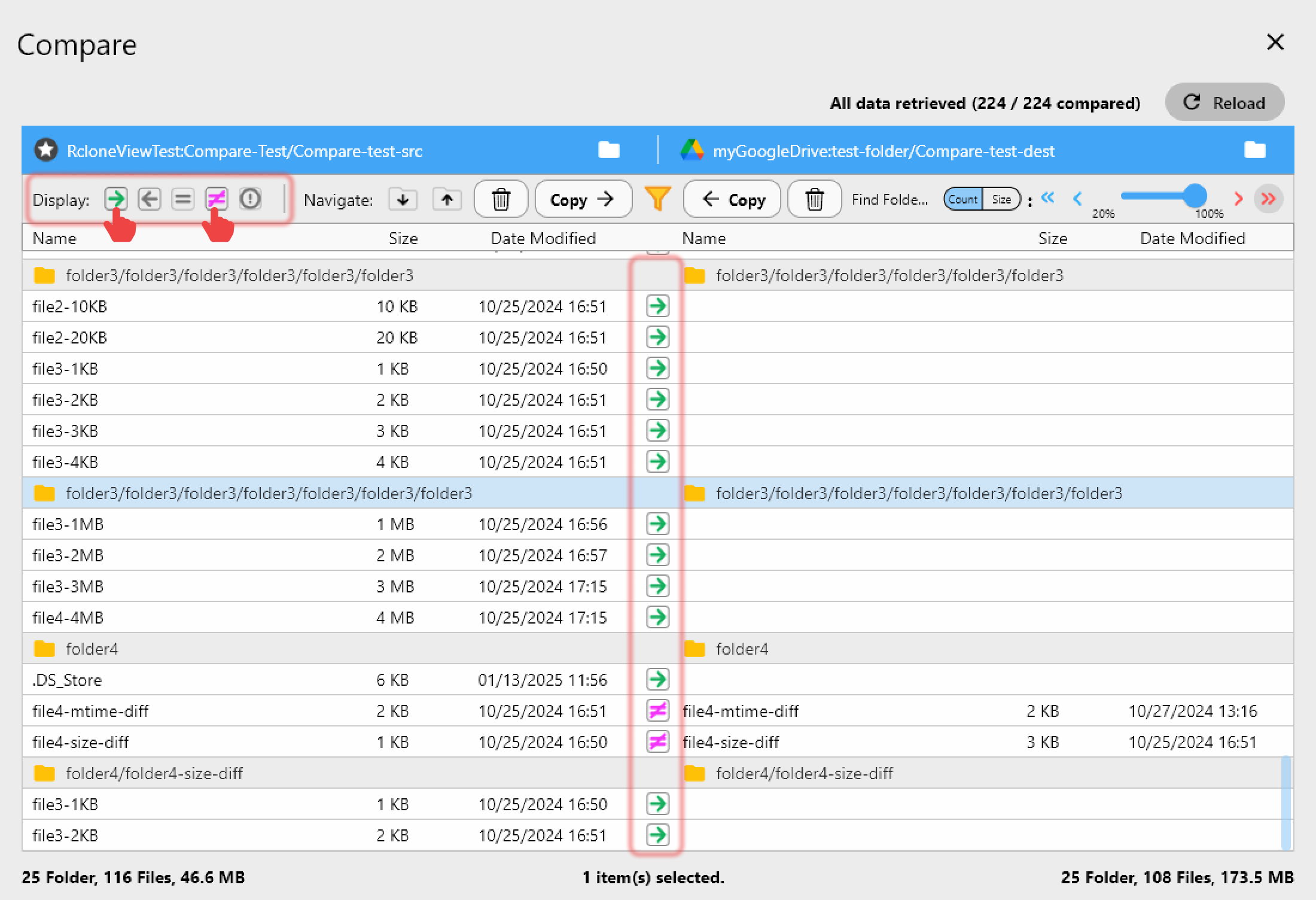
- 3.14 System and Information Integrity — identify and correct information flaws. RcloneView's compare and hash-check features let administrators verify that transferred files are bit-for-bit identical to their source, catching corruption or tampering.
Data Sovereignty and Air-Gapped Environments
Data sovereignty requirements dictate where government data can physically reside. Some agencies mandate that data remain within the continental United States, while others restrict it to specific cloud regions or even specific data centers. RcloneView lets administrators configure each remote with region-specific endpoints — for example, pointing an S3 remote to us-gov-west-1 or an Azure remote to a US Government region — so data never leaves the authorized geography.
For air-gapped or disconnected environments common in classified networks (SIPRNet, JWICS) or sensitive compartmented information facilities (SCIFs), RcloneView can operate in fully offline mode:
- Configure remotes on the air-gapped workstation pointing to local S3-compatible object stores (MinIO, Ceph, or similar).
- Transfer files between local storage and the on-premise object store using the same GUI workflow used for cloud operations.
- Export transfer logs for compliance review without any external network connection.
This approach gives analysts and administrators a consistent file management experience whether they are working on an unclassified cloud-connected network or a classified air-gapped system.
Classified vs. Unclassified Storage Workflows
Government agencies typically maintain separate infrastructure for different classification levels. A single agency might have:
- Unclassified (CUI/FOUO) — AWS GovCloud, Azure Government, or a FedRAMP-authorized SaaS provider.
- Secret — on-premise or government-owned cloud infrastructure on SIPRNet.
- Top Secret/SCI — isolated systems on JWICS or mission-specific networks.
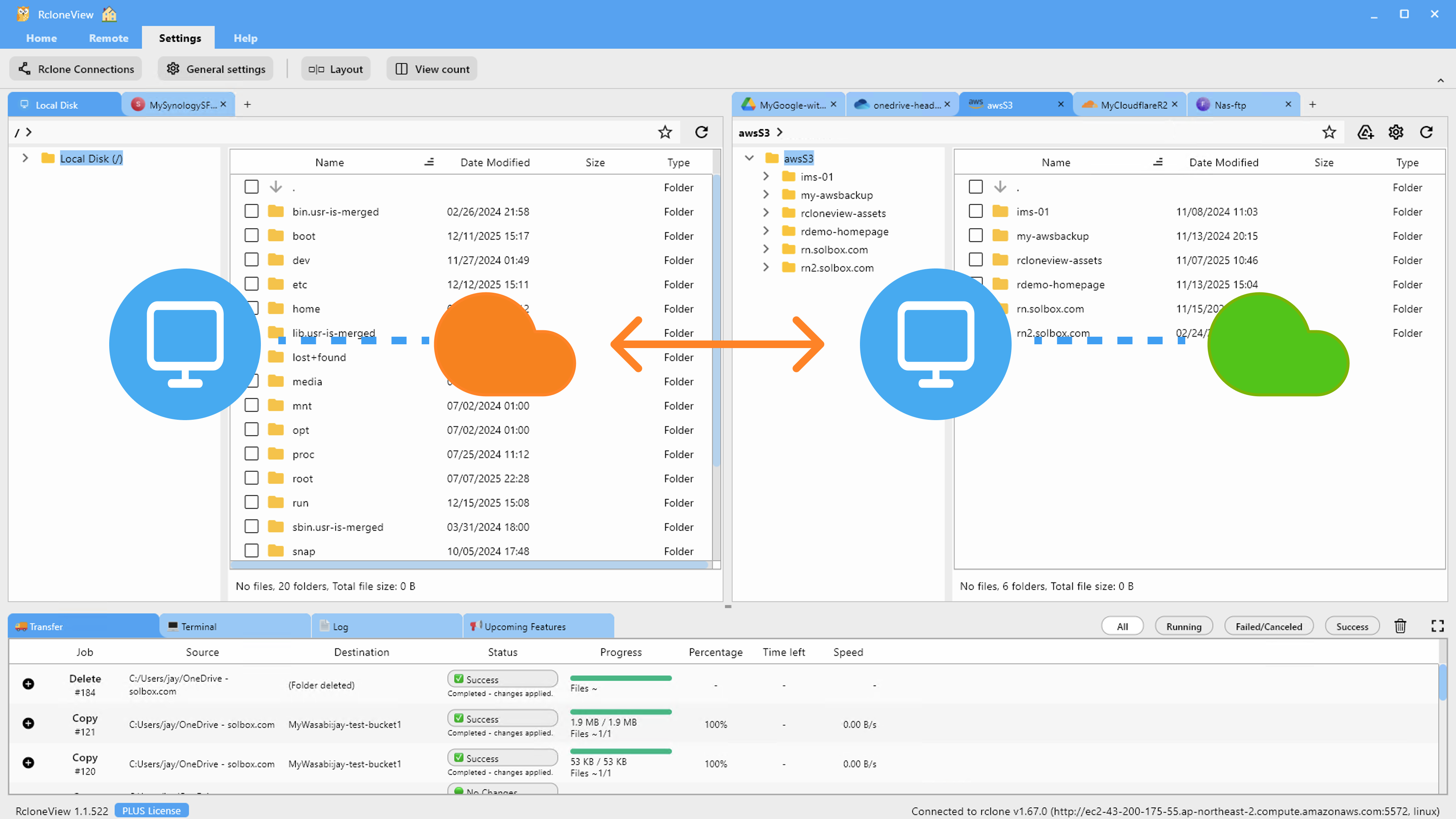
RcloneView supports distinct remote configurations for each environment. On an unclassified workstation, an administrator might configure remotes for AWS GovCloud and Azure Government. On a classified workstation, remotes might point to on-premise MinIO clusters. The workflows — browsing, transferring, comparing, syncing — remain identical across both environments.
For cross-domain transfer scenarios (moving sanitized data from a higher classification to a lower one), agencies use approved cross-domain solutions (CDS). RcloneView can serve as the file management layer on either side of the CDS, packaging files for transfer and receiving them on the other side. The tool itself does not perform cross-domain transfer — it operates within its authorized boundary and relies on the CDS for the actual boundary crossing.
Encryption Requirements and Key Management
Government encryption standards are non-negotiable. FIPS 140-2 (and its successor FIPS 140-3) validated cryptographic modules are required for protecting sensitive government data. Key considerations for using RcloneView in government environments:
- TLS for data in transit — rclone uses the Go standard library's TLS implementation. Agencies requiring FIPS-validated TLS should run rclone on a FIPS-enabled operating system (such as RHEL in FIPS mode) where the underlying crypto libraries are FIPS-validated.
- Client-side encryption — rclone's crypt backend uses NaCl SecretBox (XSalsa20 + Poly1305) for file content and AES-256-SIV (AES-EME) for file names. While these are strong ciphers, agencies requiring FIPS-validated algorithms should layer encryption through a FIPS-validated tool (such as OpenSSL in FIPS mode or a hardware security module) before transferring files with RcloneView.
- Key management — encryption passwords for crypt remotes can be stored in rclone's configuration file, which itself can be encrypted. For higher assurance, agencies can integrate with external key management systems by scripting credential injection at runtime.
Audit Trails and Cross-Agency File Sharing
When agencies share files — whether during a joint operation, an interagency task force, or a FOIA response — documentation of every file movement is essential. RcloneView provides several features that support audit requirements:
Job history — every sync, copy, or move operation is logged with timestamps, file counts, bytes transferred, and success/failure status. Administrators can review past operations and export logs.
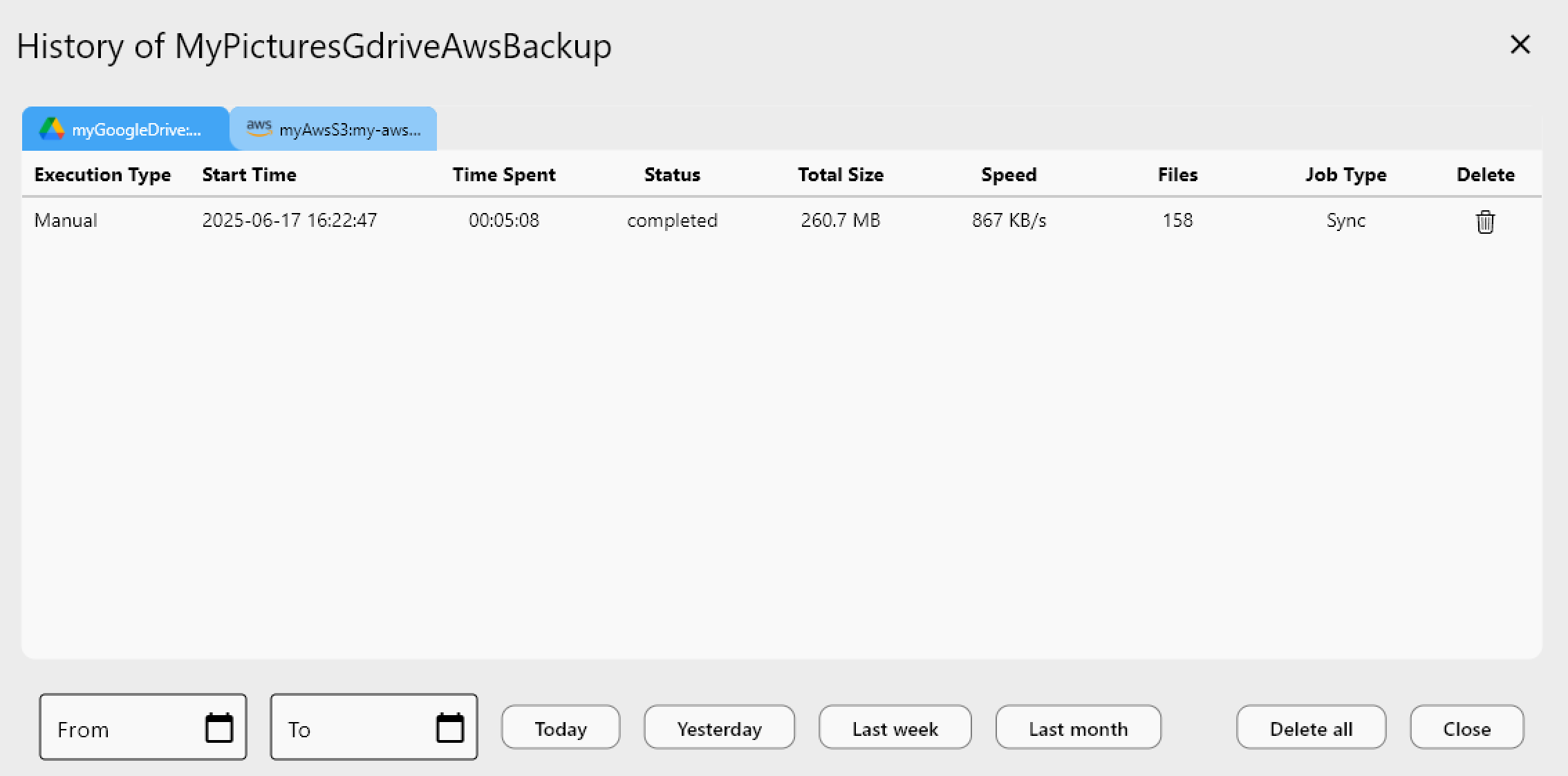
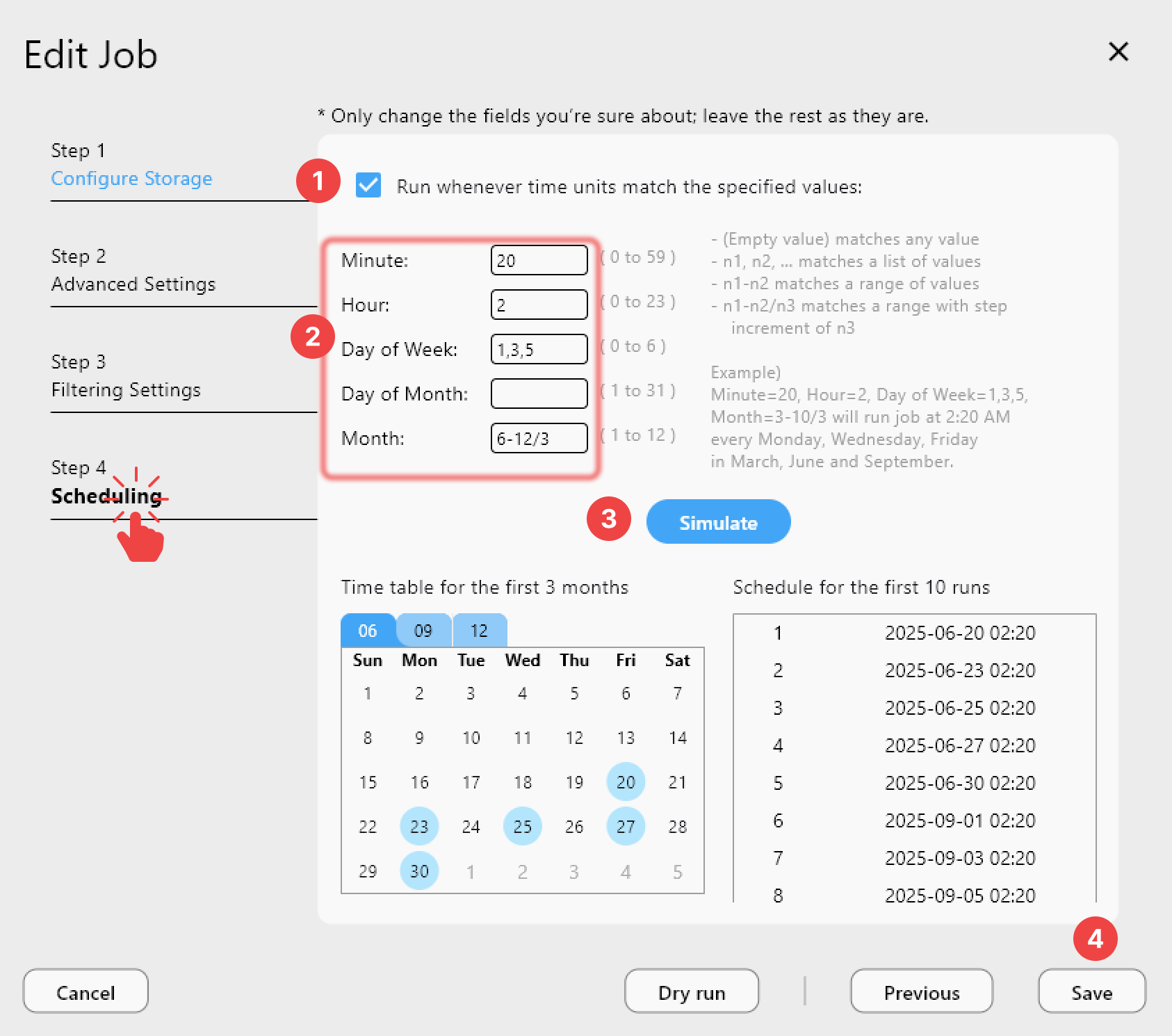
Scheduled jobs with logging — for recurring cross-agency transfers (daily intelligence summaries, weekly compliance reports), RcloneView's job scheduler runs transfers on a defined cadence and logs each execution. This creates a consistent audit trail without manual intervention.
Hash verification — after a transfer, RcloneView can compare source and destination file hashes (MD5, SHA-1, or provider-specific hashes) to confirm integrity. This satisfies chain-of-custody requirements by proving that the file received is identical to the file sent.
For cross-agency sharing scenarios, a common pattern is to use a shared S3 bucket with IAM policies that grant read access to the receiving agency's credentials and write access to the sending agency. Both agencies use RcloneView to manage their side of the exchange, and the audit logs from both sides can be correlated.
Getting Started
- Identify your authorized cloud providers — check your agency's ATO (Authority to Operate) documentation and FedRAMP marketplace listings.
- Install RcloneView on an approved workstation following your agency's software approval process.
- Configure remotes for each authorized cloud provider, using credentials issued through your agency's IAM processes.
- Set up encryption — enable client-side encryption for CUI or sensitive data using rclone crypt remotes.
- Establish audit logging — configure log export to your SIEM or GRC platform to meet FISMA audit requirements.
- Create scheduled sync jobs for recurring cross-agency or cross-system file transfers.
Government cloud storage does not have to mean government-grade complexity. RcloneView provides a straightforward, auditable, and flexible interface for managing files across any combination of authorized cloud providers — whether on an unclassified network or an air-gapped classified system.
Related Guides:
- Add Remote Storage (Google Drive Example)
- S3 Remote Storage Connection Settings
- Job Scheduling and Execution